Risk Assessment in Real Life: Where Can It Be Applied?
Risk assessment is a practical tool for everyone, not just experts. It’s used in everyday situations, like crossing the street or investing. Understanding risks can help us make better choices. Let’s explore where risk assessment applies in real life and how it helps us. It’s a part of our daily lives, whether we realize it or not.
What is Risk Assessment?
Risk assessment is the process of identifying potential hazards and analyzing the likelihood of their occurrence to mitigate and manage risk. The risk assessment app offers a practical and convenient way for companies to conduct risk assessments across various industries and improve safety protocols.
It helps organizations revamp their risk assessment programs and encourages regular risk assessments, resulting in a proactive approach to safety.
Risk assessment is used in construction to analyze hand-arm vibration syndrome (HAVS), noise risks, environmental risks, and more. Healthcare institutions benefit from health and safety risk assessment apps to comply with regulations and standards.
Manufacturers integrate mobile risk assessment technology to enhance their risk assessment procedures to address food and water contamination, product quality non-conformance, and environmental risks. In the IT sector, it aids in identifying network security threats and implementing preventive measures.
Event risk assessment apps are utilized to identify and minimize hazards like noise, weather, crowd commotion, and unstable equipment.
How Does Risk Assessment Help Us?
Risk assessment helps people and businesses make smart choices. It identifies potential risks and hazards, so preventive measures can be put in place. Regular assessments improve safety, promote a culture of safety, and reduce the chances of accidents. Integrating risk assessment into different industries brings many benefits. In construction, it addresses hazards like hand-arm vibration syndrome, noise risks, and environmental risks.
In healthcare, it ensures compliance with health and safety regulations. Manufacturers use it to manage food and water contamination, product quality issues, and environmental risks. In the chemical industry, it protects workers and the environment from hazardous chemicals. In the IT sector, it identifies network security threats. Facility safety officers use it for routine checks on ergonomics, fire risk, and stress risk.
Places Where Risk Assessment is Used
Making Buildings Safe: Risk Assessment in Construction
Risk assessment is the process of identifying, evaluating, and prioritizing potential risks or hazards within a workplace or environment. It involves the analysis of potential dangers that may harm individuals, property, or the environment.
This process helps organizations create a safe working environment, comply with regulations, and prevent accidents and injuries. By identifying and analyzing hazards, companies can implement measures to enhance safety protocols and reduce the likelihood of incidents.
In construction, risk assessment is used to analyze a wide range of potential hazards. These include hand-arm vibration syndrome , field-level hazards, flood risks, noise risks, manual handling, and environmental risks. Construction companies can ensure the safety of workers and the public by using risk assessment apps and implementing preventive measures against potential risks.
Keeping Patients Safe: Risk Assessment in Healthcare
![]()
Healthcare uses risk assessment to keep patients safe. This involves identifying potential risks and implementing measures to prevent harm. The process evaluates factors like patient safety, infection control, medication errors, and medical equipment safety. Possible risks in healthcare settings include falls, patient identification errors, surgical site infections, and staff exposure to hazardous substances.
Healthcare institutions can use risk assessment apps to ensure compliance with regulations and standards. This ultimately promotes a safe environment for patients and staff.
Product Safety: Risk Assessment in Manufacturing
Manufacturers use mobile risk assessment technology to improve their risk assessment procedures. This helps them deal with food and water contamination, product quality non-conformance, plant, and environmental risks. Risk assessment apps help manufacturers find potential hazards and reduce risks by doing regular risk assessments, which ensures product safety.
When doing manufacturing risk assessments for product safety, it’s important to consider environmental risks, product quality non-conformance, and food and water contamination.
Handling Chemicals Safely: Risk Assessment in the Chemical Industry
![]()
Risk assessment is important in the chemical industry to ensure safe handling of chemicals. It helps identify potential hazards, assess risks, and implement safety measures. When assessing risks in handling chemicals, it is important to analyze their properties and potential dangers, evaluate worker exposure levels, and determine control measures.
Best practices for managing chemical risks include implementing engineering controls, providing PPE, establishing proper handling procedures, and conducting regular employee training on chemical safety.
Keeping Information Safe: Risk Assessment in IT
Risk assessment helps in identifying and mitigating network security threats in the IT industry. It ensures the safety of sensitive information and data. Companies can use apps like ISO 27001 and IT Risk Assessment to evaluate potential risks and implement preventive measures for their software and digital assets.
IT professionals can use risk assessment apps with features like assessment process and mobile functionalities to keep software safe. These apps aid in identifying vulnerabilities, analyzing security measures, and implementing necessary changes to mitigate potential risks.
Regularly reviewing and assessing the risks associated with software in IT is important. It helps to stay ahead of emerging threats and vulnerabilities, ensuring effective security measures and minimizing the risk of data breaches and cyber-attacks. Frequent risk assessments also help in maintaining compliance with industry standards and regulations, promoting a secure IT infrastructure.
Looking After Buildings: Risk Assessment in Facilities Management
Risk assessment in facilities management is important. It helps identify and analyze potential risks that could affect building safety and the people inside. Using risk assessment apps ensures safety protocols are improved and a culture of safety is promoted.
Steps to keep buildings safe include analyzing hazards like hand-arm vibration syndrome , flood risks, noise risks, manual handling, and environmental risks.
In facilities management, risks to consider include network security threats, fire risks, environmental risks, stress risks, and hazards related to events like noise, weather, and crowd commotion.
Integrating risk assessment technology helps companies manage and address these risks to protect the health and safety of building occupants.
Planning Safe Events: Risk Assessment in Events Management
When conducting a risk assessment for events management, it’s important to consider factors such as the location of the event. Also, the type of crowd that will be in attendance, the weather conditions, and the potential hazards associated with the event setup and equipment.
Risk assessment can help to identify and mitigate potential risks in event planning. It does this by providing a systematic approach to evaluating all potential hazards and their likelihood of occurrence.
By analyzing these risks, event planners can implement appropriate safety measures. This helps to minimize the likelihood of accidents or emergencies.
Common risks to consider and assess when planning events include noise hazards, weather-related risks, crowd commotion, and unstable equipment.
Additionally, risk assessment can help to identify potential threats to the safety and security of event attendees. These include medical emergencies or unexpected disruptions.
Checking Your Software: Why You Need a Security Checklist
![]()
A security checklist helps keep your software secure. Regular checks identify vulnerabilities and threats and allow for effective measures to address them. Ensure software safety through regular updates, antivirus protection, encryption, strong passwords, and secure coding. Assessing risks highlights potential security concerns and ensures compliance with industry standards.
A risk assessment app can systematically evaluate cyber threats, privacy issues, and data breaches to enhance software security.
Steps to Keep Software Safe
Know Your Software: Gather Information
Software risk assessments help companies identify and evaluate security threats. This allows them to prioritize the safety of their digital systems and take measures to reduce these risks.
In software, a risk assessment can identify vulnerabilities and potential attack points. This includes assessing the potential impact of a security breach. Using specialized software can help pinpoint weak spots and implement preventive measures to minimize cyber attack or data breach risks.
These assessments are useful for ensuring safety and security in software development and usage. They are particularly important for network security, data protection, regulatory compliance, and identifying specific application or system risks. For instance, risk assessment applications in the IT sector help identify network security threats and implement preventive measures for digital system safety.
Set Up Systems the Right Way
Risk assessment is the process of identifying, assessing, and prioritizing risks to an organization. This helps companies improve safety protocols, compliance with regulations, and maintain a safe working environment.
The assessment is used across various industries, including construction, healthcare, manufacturing, chemical, IT, facility safety, and event management sectors. For example:
- Construction companies use risk assessment apps to analyze hazards like hand-arm vibration syndrome , field-level hazards, flood risks, and noise risks.
- Healthcare institutions use health and safety risk assessment apps for compliance with regulations and standards.
- Manufacturers integrate mobile risk assessment technology to enhance procedures and address environmental and product quality non-conformance risks.
- In the IT sector, risk assessment apps help identify network security threats.
- In event management, risk assessment apps are utilized to minimize hazards like noise, weather, crowd commotion, and unstable equipment.
Risk assessment software is a vital tool for many companies, offering features such as the assessment process and mobile functionalities for convenience and efficiency.
Who Can Get In?: Manage Identity and Access
Access to areas and information in an organization is based on the roles and responsibilities of individuals. In healthcare, only medical staff can access patient records and sensitive medical info. In IT, sensitive info access is managed through role-based control, assigning permissions based on job function.
Measures to control identity and access include unique user IDs, strong passwords, multi-factor authentication, and regular access reviews. Some organizations use biometric access control systems.
Access to sensitive areas or info is determined and monitored through access control lists, user activity logs, and real-time monitoring systems. In manufacturing, access to production areas is restricted to authorized personnel. Unauthorized attempts to access these areas are immediately flagged and investigated.
Check How Users Sign In: Revisit Authentication
Users sign in to the risk assessment app using a two-factor authentication process. First, they enter a password. Then, they verify their identity through a one-time code sent to their registered mobile device.
This method ensures added security and protects sensitive data from unauthorized access. The app also offers biometric authentication options like fingerprint and facial recognition for users with compatible devices, making the sign-in process convenient and secure.
The app incorporates multi-factor authentication, password requirements, and periodic forced password resets for user sign-in. These measures minimize the risk of unauthorized access and data breaches, ensuring the confidentiality and integrity of risk assessment records and reports.
However, there are potential vulnerabilities or weaknesses in any authentication process. For example, users might fall victim to phishing attacks, leading to compromised login credentials. To address this, the app provides regular security awareness training for users to recognize and report phishing attempts, strengthening the overall security of the authentication process.
Keep Your Software Parts Safe: Secure the Supply Chain
Securing the supply chain is important for keeping software parts safe. It helps prevent unauthorized access, data breaches, and malware infections, preserving the integrity of the software. By securing the supply chain, companies can ensure that only trusted and verified components are used in the software development process, reducing the risk of vulnerabilities and cyber-attacks.
To secure the supply chain and protect software parts, companies can take steps like implementing strict vendor selection criteria, conducting thorough background checks on suppliers, enforcing cybersecurity best practices, and regularly auditing the entire supply chain for any potential security gaps or weaknesses.
A risk assessment can help in identifying potential threats to the supply chain and software security. It evaluates vulnerabilities and potential risks associated with each component or supplier. This assessment can uncover any weaknesses in the supply chain that could be exploited by malicious actors, allowing companies to take proactive measures to secure their software parts and prevent any security breaches.
Take Out Private Info from Code
To remove private information from code, developers can start by reviewing the code thoroughly. They should look for any personal data like identification numbers, email addresses, or financial information. Then, they can use automated tools to scan the code for any potential leaks of private information and remove or redact the data as necessary.
Developers should also avoid hardcoding private information directly into the code. This makes it more vulnerable to exposure. Instead, they can use best practices for secure coding. This includes using environment variables or configuration files to store sensitive data separately from the codebase.
To protect private data, developers can implement access controls, encryption, and regularly conduct code reviews and audits.
Leaving private information in code poses risks such as unauthorized access to sensitive data, data breaches, compliance violations, and damage to the organization’s reputation. This can result in financial losses, legal repercussions, and loss of trust from customers and stakeholders.
Lock Up Data: Use Encryption
Encryption is a way to turn data into a secret code. This helps prevent unauthorized access. It uses complex algorithms to scramble the information. Only those with the encryption key can decrypt it.
Best practices for using encryption to protect sensitive information include:
- Implementing strong, industry-standard encryption algorithms.
- Using secure and unique encryption keys.
- Regularly updating encryption protocols.
It’s crucial to ensure that all devices and communication channels are encrypted, such as mobile devices and email systems. This is important for protecting sensitive data.
Encryption also helps in maintaining compliance with data protection regulations and standards, like HIPAA and GDPR. It provides a secure method for storing and transmitting sensitive information.
For example, in the healthcare industry, patient records and medical histories must be encrypted to protect patient privacy. Similarly, financial institutions use encryption to safeguard customer financial information and transactions, maintaining trust and security for their clients.
Test the Business Side of Software
Risk assessment in software development is important. It helps identify security threats and vulnerabilities. This is crucial for ensuring safety and security. Companies can evaluate the potential impact of security risks and take necessary measures to prevent them. They can identify key areas of vulnerability, like network security threats and environmental risks. Using risk assessment apps, companies can identify potential security threats and perform routine checks to protect the software.
This includes evaluating risks related to network security, stress, and fire. Risk assessment apps provide companies with tools to identify, evaluate, and mitigate potential security risks and vulnerabilities in software development.
Check the Software’s Front End
The front end of a software has key security elements. These should be checked regularly for security. They include:
- User interface design
- Input validation
- Authentication controls
- Error handling
These elements are important in preventing unauthorized access and protecting sensitive data. They also ensure the overall security of the application.
Regular security audits, penetration testing, and code reviews can help identify and address potential vulnerabilities. By evaluating the front end components thoroughly, developers can find security loopholes and fix them.
To make sure a software’s front end is secure, developers can:
- Use secure coding practices
- Stay updated with security patches and updates
- Educate users about best security practices
Additionally, integrating security features like encryption, multi-factor authentication, and secure session management can further strengthen the front end security of the software.
What If Something Goes Wrong? Review Error Handling
When something goes wrong with software, it’s important to review error handling. This helps find the root cause of the issue, assess its impact, and take corrective actions.
How to improve error handling and ensure software safety and security:
- Conduct regular risk assessments
- Identify and prioritize potential risks
- Implement preventive measures
Inadequate error handling in software systems can lead to risks such as data breaches, system failures, financial losses, and compromised user safety. For instance, a risk assessment app with poor error handling could result in inaccurate risk data, leading to incorrect safety protocols and increased safety risks for workers and the environment.
As a result, effective error handling is crucial for maintaining the integrity and reliability of software systems across various industries.
Make Software Safer with a Risk Assessment
Risk assessment helps make software safer by identifying security risks and vulnerabilities. Companies can proactively address security concerns and implement measures to mitigate those risks, improving the overall safety and security. It analyzes system vulnerabilities, potential data breaches, and cyber threats. Companies should establish a comprehensive risk assessment process, conduct regular assessments, and integrate risk assessment tools into their software development lifecycle.
This ensures potential security risks are continually evaluated and addressed, leading to a safer software application.

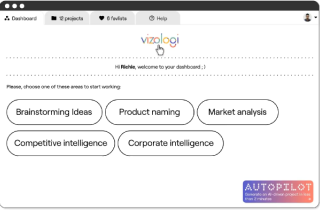
Vizologi is a revolutionary AI-generated business strategy tool that offers its users access to advanced features to create and refine start-up ideas quickly.
It generates limitless business ideas, gains insights on markets and competitors, and automates business plan creation.